内核数据结构
Linux内核中实现了一些常见的数据结构,而且内核要求代码越高效越好,所以这些数据结构的实现极为优雅!因此,千万不要自己实现山寨的数据结构。
内核的数据结构包括:
- 链表(双向循环)
- 队列
- IDR & IDA
- 红黑树
链表
链表头文件
位于include/linux/link.h
qemu相比于vmware,简单、轻便,可以直接指定linux内核,再指定一个文件系统,即可调试。硬盘、网络设备可以后加。
首先我尝试了utmapp/UTM,这是个适用于iOS/macOS的虚拟机,基于qemu。但是在指定内核启动镜像bzImage和initramfs后,遇到了问题,一直报错:
1 | The bootindex 0 has already been used |
搞了一会没搞出来,索性不用UTM了,直接上qemu。
使用homebrew可以直接安装qemu。
1 | ➜ ~ brew install qemu |
目前安装的是7.0.0_2。
安装完成之后验证一下:
1 | ➜ ~ qemu-system-x86_64 --help |
rootkit is another challenge about kernel exploits after syscall.
After connected to host, I found that the kernel load rootkit module at boot.
1 | [ 3.337631] rootkit: module license 'unspecified' taints kernel. |
Then, I use ida to disassembly the rootkit.ko.
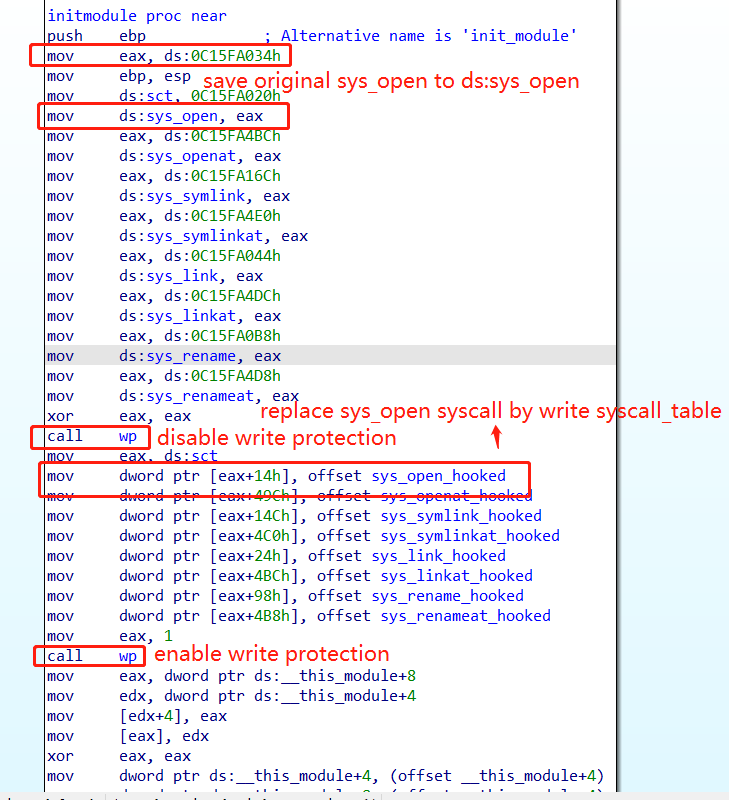
The module disable write protection, and replace original syscall such as sys_open to sys_open_hooked by write syscall table(0xc15fa020).
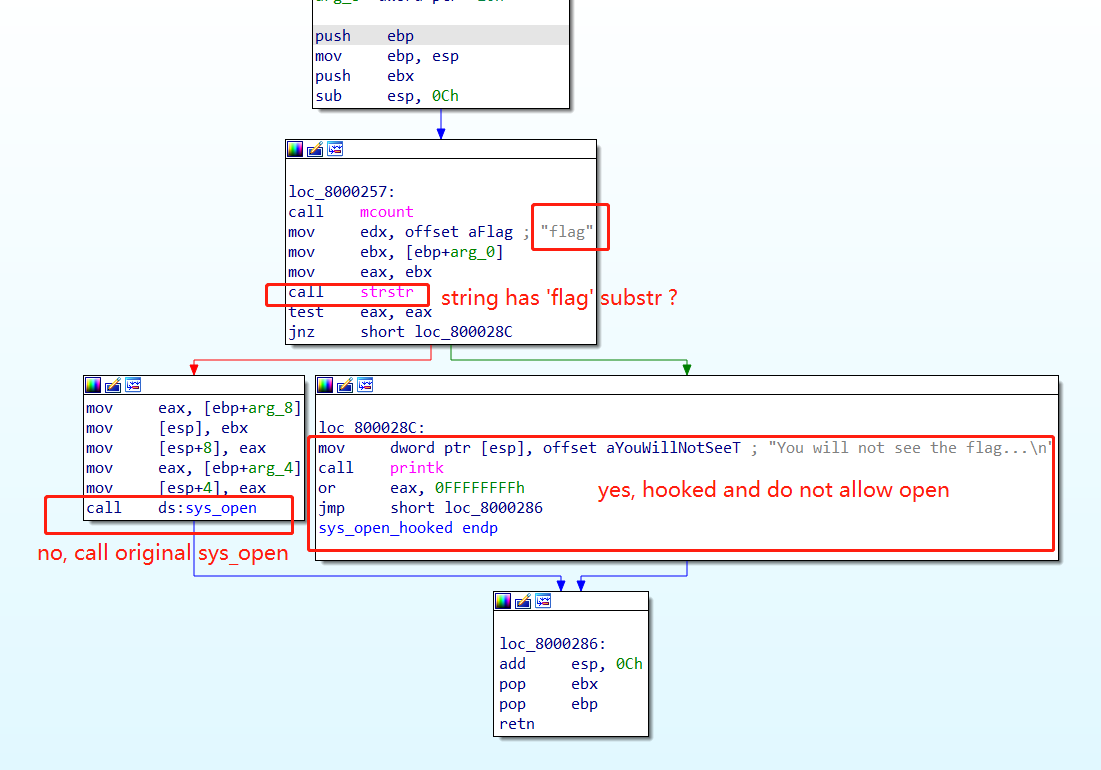
The sys_open_hooked syscall will check whether the string of the filename has a flag substring.
If there not, then the original sys_open is called.
If there is, it returns a fd with a value of -1, then the file opening failed.
Of cource, other sys_call such as sys_symlink will failed also.
1 | /tmp # ln -s ../flag ./ |